Network Security and Compliance
Monitor and investigate security incidents across all your networks.
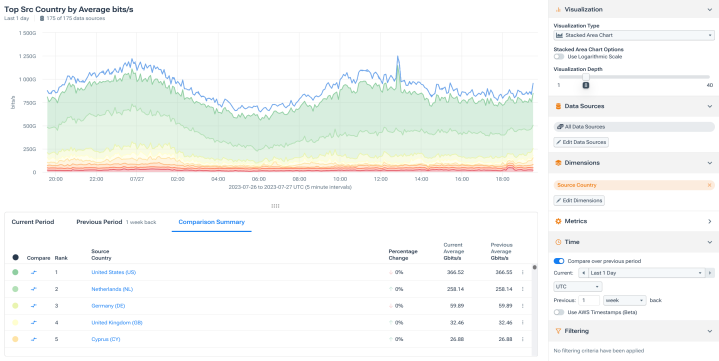
AI-driven anomaly detection
- Identify network-probing behavior across your network.
- Audit unusual internet traffic.
- Detect traffic to or from embargoed countries.
Quickly detect DDoS attacks with confidence
- Minimize false positives and negatives with advanced detection algorithms.
- Customize out-of-the-box attack profiles.
- See across all networks in real time.
Streamline attack response
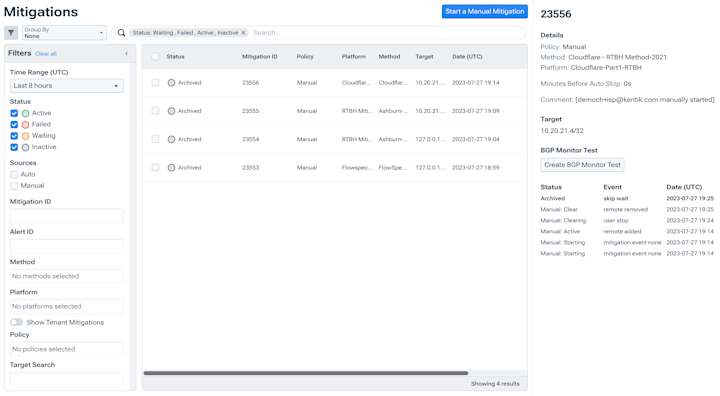
- Mitigate attacks using your own infrastructure via RTBH/Flowspec.
- Invoke mitigation through integrations with providers like Cloudflare, Radware, and A10.
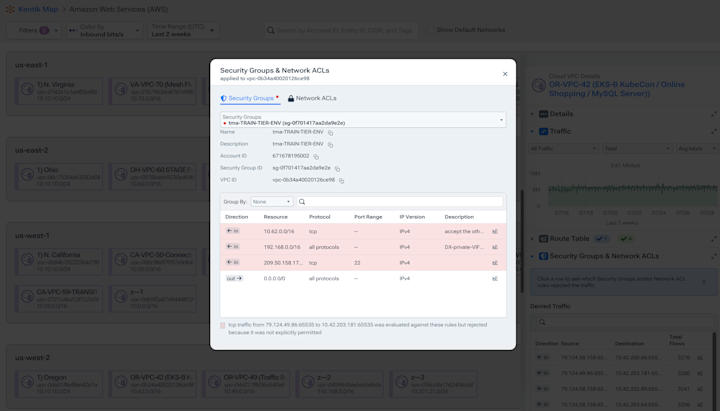
Validate policy compliance
- Identify and alert on rejected traffic anomalies.
- Verify RPKI enforcement.
- Validate cloud ACLs.
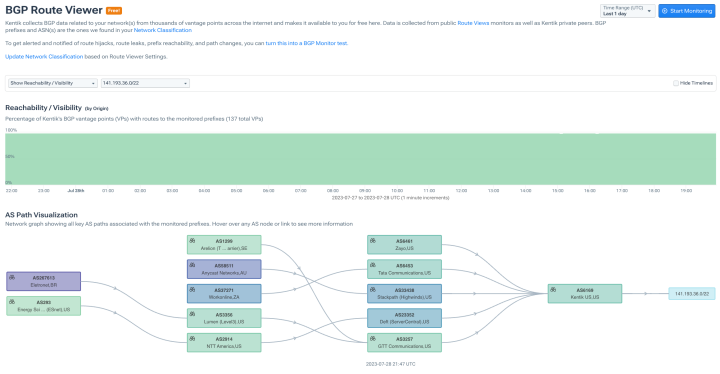
Detect mis-routed traffic
- Find BGP leaks and hijacks.
- Test BGP reachability.
- Track BGP route changes.
Identify malware communication
- Alert in real time on blacklisted IPs and domains.
- Audit traffic to and from prohibited geographies.
- Filter out VPC black holes.
Full fidelity forensics
- Understand historical data exfiltration/infiltration.
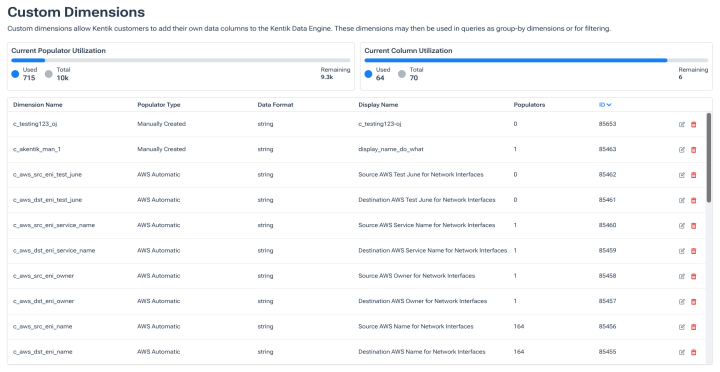
- Determine what accessed the network with security and business enriched.
- Identify users with ID enriched flow data.

“In a DDoS attack you want to look at traffic volumes, but with Kentik we also can look at source IPs, AS numbers, and other metrics to see if it’s a distributed attack. This is so easy to do in Kentik.”
Explore solutions
FAQs about Kentik Network Security and Compliance
What network security and compliance capabilities does Kentik provide?
Kentik provides a unified set of network-layer security and compliance capabilities built on full-fidelity flow telemetry: AI-driven anomaly detection for probing, reconnaissance, and unusual traffic patterns; DDoS detection and automated mitigation via RTBH, Flowspec, or third-party scrubbing services (Cloudflare, Radware, A10); BGP route hijack and leak detection with RPKI validation; policy compliance verification through rejected-traffic analysis and cloud ACL audits; malware communication detection via blacklist matching and prohibited-geography auditing; and full-fidelity forensic data retention for breach investigation. These capabilities work as part of the broader Kentik network intelligence platform rather than as a standalone security product, which makes them especially useful for network teams that need security-aware analytics on the same data they use for performance and capacity work.
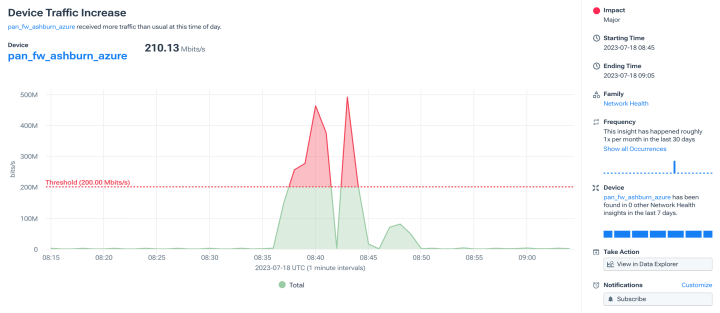
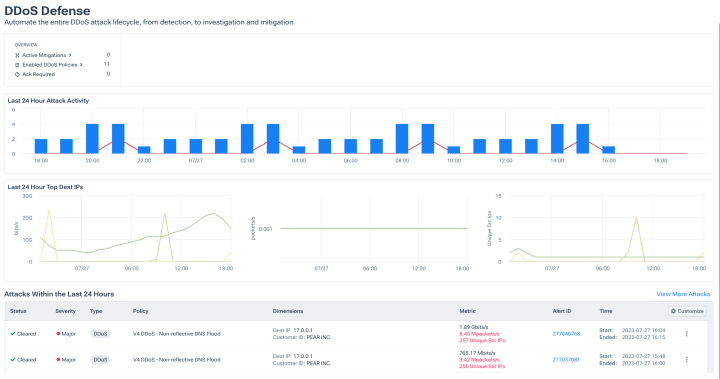
How does Kentik detect DDoS attacks and trigger mitigation?
Kentik’s DDoS detection uses configurable attack-profile algorithms — including baseline-deviation detection, volumetric thresholds, and pattern-matching against known attack signatures — applied to full-fidelity flow data across on-premises and cloud environments in real time. When an attack is detected, mitigation can be triggered automatically through several paths: self-mitigation via RTBH (remotely triggered black hole) or BGP Flowspec announcements to your own infrastructure, or invocation of cloud-based scrubbing services through integrations with Cloudflare, Radware, A10 Thunder TPS, and others. Teams customize attack profiles to minimize false positives and tune detection for their specific traffic patterns. For broader context on DDoS detection methodology, see Kentik DDoS Protection Solutions.
How can I monitor firewall policy impact on application performance?
Firewall policies often affect application performance in ways that are hard to attribute — blocked traffic, increased latency from deep packet inspection, asymmetric routing through firewalls, or rule misconfigurations that drop legitimate traffic. Kentik supports this by ingesting flow data from network firewalls (including AWS Network Firewall, Azure Firewall, and traditional vendor firewalls) and correlating allowed and denied traffic with application performance metrics. Security and network teams use this combination to identify which firewall rules are blocking legitimate application traffic, where policies are creating unexpected performance bottlenecks, and which rules are no longer needed because no traffic is hitting them.
How can I ensure zero-trust policies are enforced at the network layer?
Zero-trust enforcement at the network layer requires the ability to verify that traffic actually flows according to policy — not just that policy is configured correctly. Kentik supports this by capturing east-west and north-south flow data across data center, cloud, and Kubernetes environments, then comparing observed traffic patterns against intended segmentation policy. Teams can identify segmentation violations (traffic between workloads that policy says shouldn’t communicate), unexpected service-to-service connections, and policy gaps where critical assets are reachable from environments they shouldn’t be. The combination of flow visibility with business-context enrichment makes it possible to validate zero-trust posture continuously rather than only during periodic audits.
How do I ensure compliance with segmentation policies across hybrid environments?
Segmentation compliance across hybrid environments requires consistent visibility into traffic between segments regardless of which environment a segment lives in — on-premises VLANs, AWS VPCs, Azure VNets, GCP VPCs, OCI VCNs, or Kubernetes namespaces. Kentik provides this unified view by ingesting flow data from all of these environments into a single platform and tagging each flow with the segment, application, and business context it belongs to. Compliance teams can verify that segmentation policies are enforced consistently, surface violations across environment boundaries, and produce audit-ready reports showing which traffic crossed segmentation boundaries during any given time period.
What capabilities support compliance reporting for network access and flows?
Network compliance reporting typically requires evidence of traffic patterns (who communicated with whom, when, and through which network paths), enforcement of access controls (which traffic was permitted vs. denied), and forensic reconstruction capability for incident response. Kentik supports compliance reporting through full-fidelity flow retention (120 days standard, with longer retention available for specific compliance regimes), enriched flow records that include geographic, AS path, security, and business context, customizable dashboards and reports that can be exported for auditors, and APIs that let compliance tooling consume the underlying data. The platform supports common compliance frameworks (SOC 2, PCI DSS, HIPAA, GDPR) through evidence that flow data exists to verify network access patterns over time.
How does Kentik detect BGP route hijacks and leaks?
BGP hijacks and leaks occur when another network announces prefixes it shouldn’t, redirecting traffic through unexpected paths. Kentik detects these events through continuous monitoring of BGP routes against expected origin ASNs and prefix ownership, integration with RPKI validation to verify route authorization, real-time alerting when unauthorized announcements appear in the global routing table, and forensic analysis of past routing events with full historical context. Network teams use this to detect hijacks affecting their own prefixes (defensive monitoring), identify when traffic is being routed through unexpected paths, and track the impact of leaks on their traffic. For Kentik’s broader BGP capabilities, see BGP Route Monitoring.
What’s the difference between investigating security incidents and the broader Network Security and Compliance product?
The Investigate Security Incidents solution focuses on workflow — how investigators use Kentik during and after an incident to reconstruct what happened, identify the source of suspicious traffic, and produce forensic evidence. The Network Security and Compliance product covers the broader set of capabilities Kentik provides for ongoing security and compliance posture — AI-driven anomaly detection, DDoS detection and mitigation, BGP hijack monitoring, policy compliance validation, and the underlying flow analytics that support all of these. Most teams use both: the product capabilities for continuous monitoring and posture validation, the investigation workflows when an incident occurs. For incident-response specifics, see Investigate Security Incidents.